When Independence Becomes Isolation
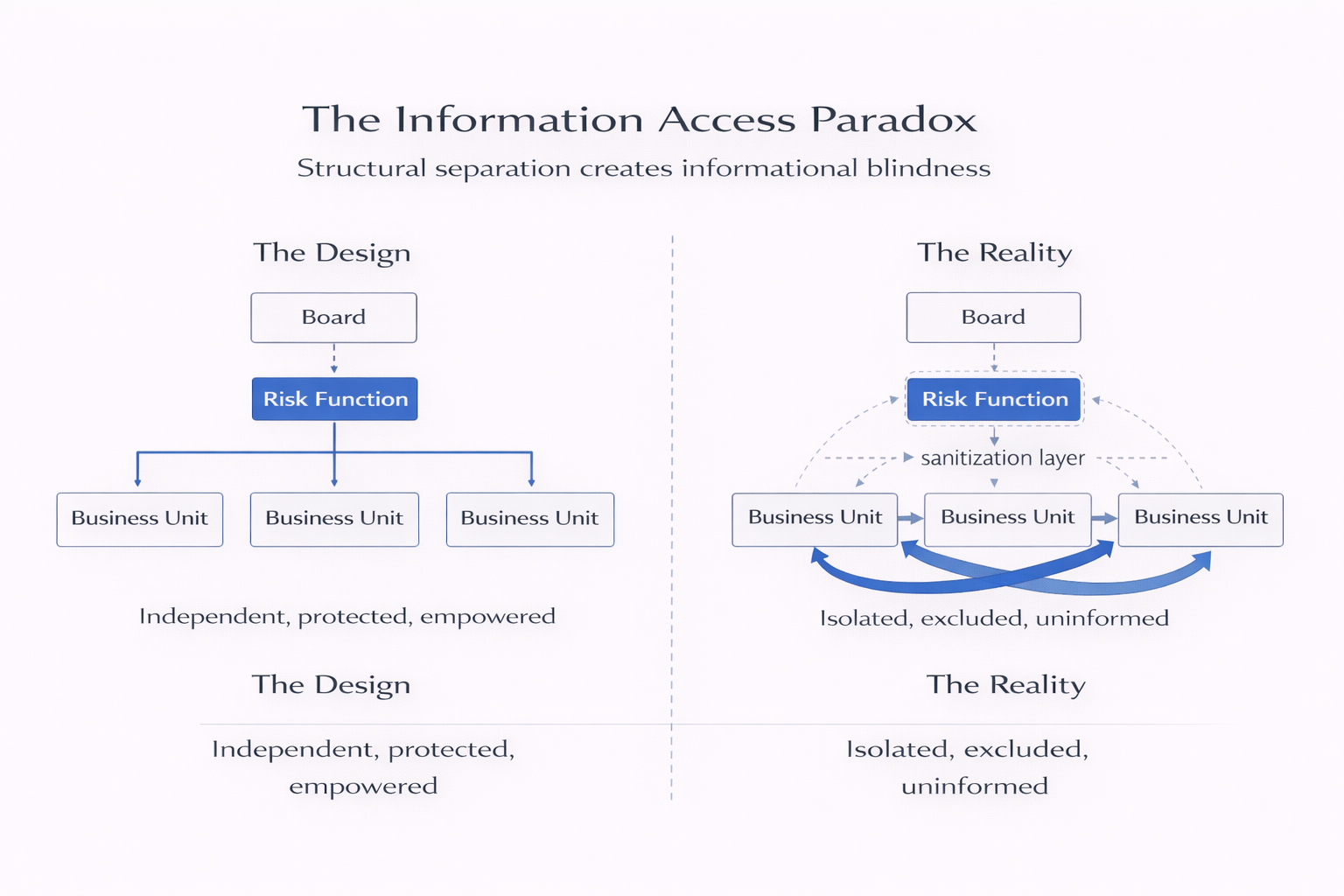
Part 1 - Formal independence solves conflict of interest but creates information blindness. When risk functions become structurally separate, business units shift from sharing context to managing exposure. Risk teams see polished versions of problems already contained—by design, not accident.
Risk Judgment Series
How Risk Teams Actually Fail
Risk functions are designed with sound logic—independence, expertise, board access. Then reality surfaces predictable failure patterns. This series examines how organizational structure, not incompetence, systematically undermines risk teams. Part 1 of 6.
The risk team discovers a trading loss three days after legal gets involved. Not because they weren’t watching. Because nobody told them.
By the time the CRO hears whispers, the breach has been contained, the traders reassigned, the incident report drafted. The risk function had independence. Board access. Oversight authority. What it didn’t have was a reason for anyone to call.
This isn’t about incompetence or bad faith. It’s about structure.
Organizations design risk functions to be independent—separate from business pressure, free to speak truth, protected from conflicts of interest. The logic is defensible. The org chart looks right. The governance framework passes regulatory review.
Then reality surfaces a pattern: the very independence meant to give risk teams power systematically cuts them off from the information they need to exercise it.
I’ve watched this play out across financial services, technology, healthcare, energy. The sectors differ. The mechanism doesn’t.
The Design Logic
Independence solves a real problem. Business units face pressure to deliver—revenue targets, product launches, operational efficiency. When risk oversight sits inside those units, the pressure bleeds into risk judgment. Conflicts multiply. Uncomfortable assessments get softened. Escalations get delayed.
So organizations separate the risk function. Independent reporting lines. Direct board access. Formal authority to challenge business decisions. The structure says: this team answers to no one but truth.
It’s a rational response to a structural conflict. It also introduces a different, less visible one.
Because the moment you make the risk function independent, you change how the rest of the organization relates to it. The team is no longer “us” making hard calls together. It becomes “them”—the auditors, the overseers, the people who slow things down.
Business units don’t share information with auditors. They manage it.
The Reality Pattern
I’ve watched this unfold the same way across contexts. The risk function gets its independence. The governance documents get written. The org chart gets updated.
Then the information environment shifts.
What used to flow informally—hallway conversations, early warnings, messy uncertainties—starts getting filtered. Business units become deliberate about what risk sees. Problems get framed as solved before risk hears about them. The messiest, earliest signals—the ones that matter most—never make it to the risk team’s desk.
Not because anyone is hiding failures. Because the structural incentive is to present competence, not uncertainty.
When risk is embedded, messiness is shared context. When risk is independent, messiness is exposure.
So the risk team sees polished versions. Board presentations. Incident reports written after containment. Metrics that lag reality by weeks. By the time risk gets visibility, the pattern is established, the decisions made, the momentum irreversible.
The team has formal authority. What it doesn’t have is informal access to the detail of what’s actually happening.
The Mechanism
The mechanism is deceptively simple: formal independence creates informal exclusion.
When you’re structurally separated, you’re not in the room where problems surface. It shows up in the earliest, least formal conversations—long before anything is written down. You’re not in the Slack channel where the product team realizes the launch timeline is impossible. You’re not on the call where the traders first notice the limits feel uncomfortable. You’re not at the meeting where engineering says the third-party integration is behaving strangely.
You get the sanitized version three steps later, after the problem has been reframed as manageable.
This isn’t malice. It’s rational behavior responding to structural incentives. Business units know the risk team’s job is to challenge, escalate, slow down. So they wait until they have a clean story before bringing risk into the conversation. By then, the messy early signals—the uncertainty, the ambiguity, the “something feels off”—are already interpreted, packaged, resolved.
Risk sees the conclusion. It missed the evolution.
And this compounds over time. The more often risk shows up late, the less valuable the business perceives the function to be. The less valuable risk seems, the less reason anyone has to include them early. Independence becomes isolation. Isolation becomes irrelevance.
I’ve watched risk functions with impeccable governance frameworks become the last to know about the risks that mattered most—not because they weren’t looking, but because the structure ensured they were looking in the wrong direction.
The Information Access Paradox
Formal independence creates informal exclusion. The structural separation designed to give risk teams power systematically cuts them off from the early, messy signals they need to exercise it.
The Consequence
The cost isn’t just delayed visibility. It’s that the risk function optimizes for the wrong inputs.
When you can’t access early, messy signals, you gravitate toward what you can measure: metrics, reports, formal assessments. You build dashboards. You track KPIs. You analyze what’s quantifiable and documented.
All of which lags reality.
The trading desk that’s quietly pushing boundaries doesn’t show up in your risk dashboard until the breach. The product decision that’s creating liability doesn’t surface in your metrics until the lawsuits. The operational shortcut that’s eroding resilience doesn’t appear in your reports until the failure.
You’re not measuring risk. You’re measuring the documented artifacts of decisions already made.
Meanwhile, the organization believes it has robust oversight. The risk function has independence. It has board access. It has a mandate. The governance looks strong.
What nobody sees is that the information the risk team is working with is systematically lagged, filtered, and sanitized by the very structure designed to empower them.
So when the crisis hits, everyone asks the same question: Why didn’t the risk team see this coming?
The answer is structural. They were designed not to.
📌 Key Takeaways:
- 1️⃣ Independence changes perception: When risk functions become structurally separate, business units shift from sharing context to managing exposure.
- 2️⃣ Information gets filtered systematically: Early, messy signals—the ones that matter most—are interpreted and packaged before risk teams see them.
- 3️⃣ Formal authority doesn't guarantee informal access: Risk teams end up optimizing for lagged metrics rather than real-time intelligence.
- 4️⃣ This is a structural pattern, not a behavioral one. Better communication can't fix what organizational design has embedded.
The Pattern Isn’t Fixable by Exhortation
The pattern is structural, not fixable by exhortation. You can’t solve the Information Access Paradox with “better communication” or “more engaged stakeholders.”
When independence is written into governance frameworks, mandated by regulation, and reinforced by organizational reflexes that protect business units from oversight, the information gap isn’t a bug. It’s the design working exactly as built.
Risk functions remain independent. Business units remain guarded. And the organization remains confident in its governance—right up until the moment when the risk team’s isolation becomes visible through crisis.
By then, of course, everyone wonders why the risk team didn’t see it coming.
They were designed not to.
Frequently Asked Questions
For readers seeking quick answers to common questions about risk function independence and the Information Access Paradox:
Doesn’t independence protect risk teams from business pressure?
It does—but it also changes how business units relate to risk oversight. The same structural separation that prevents conflicts also creates information barriers. Organizations trade one risk (compromised judgment) for another (delayed visibility).
Can risk functions overcome this through better stakeholder relationships?
Individual relationships can improve access at the margins, but they don’t change the structural incentive. When risk is formally independent, business units remain rationally cautious about what they share, regardless of personal trust.
Is this pattern unique to certain industries or organization type?
No. I’ve observed it across financial services, technology, healthcare, energy, and manufacturing. The sectors vary, but the mechanism—formal independence creating informal exclusion—remains consistent.
What signals indicate a risk function is experiencing this pattern?
Risk teams learning about problems after they’ve been contained. Incident reports arriving fully formed rather than emerging through dialogue. Reliance on metrics and dashboards that consistently lag real-time concerns.
Don't Miss the Next Post
This is Part 1 of a 6-part series examining how risk teams fail—not through incompetence, but through structural design.
Next: Why risk functions optimize for compliance theater instead of strategic insight, and how measurability bias creates the illusion of oversight.
New posts every week. Unsubscribe anytime.
Related Reading:
- When Governance Becomes a Substitute for Judgment: How organizations build elaborate risk frameworks that create the appearance of control while actual judgment quietly disappears.
- Risk Escalation Fails Long Before Anyone Raises Their Voice: Why formal escalation paths exist on paper but fail in practice—and what this reveals about organizational power dynamics.
- The Meeting After the Meeting: Where real decisions happen when risk leaders aren’t in the room—and why formal authority doesn’t guarantee informal influence.
Independence solves the conflict of interest problem. It creates the information problem. Most organizations only measure one.
