Dependency Risk: The Exposure No One Owns
Part 4 - Some risks don't sit in any category. They live in what you assume will continue—availability, responsiveness, stability. Dependency risk doesn't announce itself. It presents as infrastructure. Until something stops working.
🌟 RISK JUDGMENT SERIES: The Practice of Uncertainty — Part 4 of 4
This is Part 4 of “The Practice of Uncertainty”—a series on how risk leaders operate effectively when certainty isn’t coming.
Sensemaking reveals what matters. Understanding where decisions happen and how to translate uncomfortable truths creates traction. Now: what becomes visible when you stop organizing risk by category and start asking what you’re depending on.
Some of the most consequential risks don’t sit in any risk category.
They don’t appear on heatmaps. They aren’t owned by a function. They rarely trigger escalation until something stops working.
Yet entire institutions depend on them.
This is dependency risk: exposure created not by what you do, but by what you assume will continue.
In complex institutions, these assumptions often sit beneath strategy, governance, and operations—unexamined, yet consequential.
The Risk That Lives Between Categories
Most risk frameworks are built around ownership.
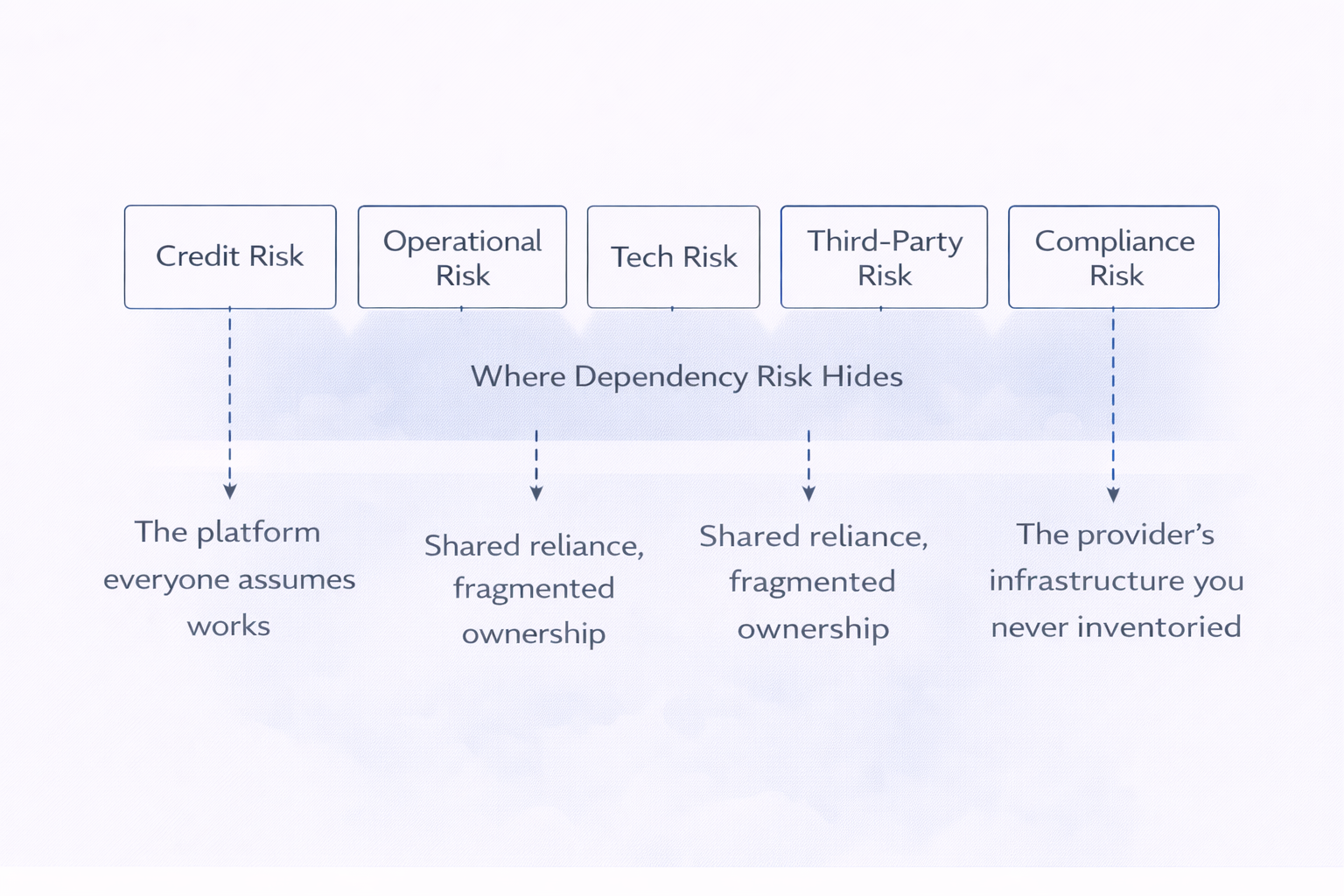
Credit risk has a home. Operational risk has controls. Technology risk has roadmaps. Third-party risk has registers.
Dependency risk sits between them.
It emerges where responsibility fragments, where reliance is shared but accountability is not. One function manages the contract. Another manages performance. A third assumes continuity. No one owns the exposure created by the dependency itself.
As long as everything works, this feels efficient.
When it doesn’t, it feels like a surprise.
Why Dependency Risk Is So Easy To Miss
Dependency risk hides in plain sight because it looks ordinary.
It looks like the core platform no one remembers choosing but everyone assumes will be available. The provider that sits quietly behind multiple functions, treated as non-strategic because it’s ubiquitous. The manual workaround that became permanent because it never broke. The decision point that exists on paper but not at 3 a.m. when it’s needed.
It doesn’t announce itself as a risk. It presents as infrastructure.
And because it cuts across categories, it is often treated as someone else’s detail. Too operational for strategy. Too strategic for operations. Too embedded to be challenged without friction.
Smart institutions miss it not through negligence, but through classification.
"Dependency risk doesn’t announce itself as a risk. It presents as infrastructure—ordinary, assumed, essential."
Modern Institutions Are Built On Assumptions Of Continuity
What makes dependency risk hard to see is not ignorance, but normalization.
Dependency risk is not primarily about failure. It’s about assumption.
Modern organizations are layered on systems and providers expected to remain stable, invisible, and sufficient. Availability is assumed. Responsiveness is assumed. Neutrality and scale are assumed. These assumptions are rarely articulated because they rarely need to be—until they do.
The exposure doesn’t arise when something breaks.
It arises when the institution quietly builds around the belief that it won’t.
When Dependency Becomes Visible
Dependency risk reveals itself late.
Often at the moment when escalation pathways narrow instead of widen, decision rights are unclear, and options are fewer than expected.
What looked like a background reliance becomes a front-stage constraint.
At that point, the question is no longer who manages this, but how much depended on it—and whether the organization understood that dependence in advance.
"The exposure doesn’t arise when something breaks. It arises when you’ve quietly built around the belief that it won’t."
Why Governance Struggles With Dependency
Governance systems are designed to oversee activities, controls, and owners.
Dependency risk challenges all three.
It is not an activity. It does not map cleanly to controls. It often lacks a single owner.
Reporting tends to track what is managed, not what is relied upon. Assurance assumes independence where interdependence has quietly grown. Oversight focuses on compliance with frameworks rather than exposure created between them.
As a result, dependency risk is rarely denied. It is simply not surfaced clearly enough to be owned.
A Different Question To Ask
Dependency risk does not require new taxonomies or complex modeling to become visible.
It requires a different question.
Not: “What risks are we managing?”
But: “What are we depending on that would surprise us if it stopped working?”
That question doesn’t fit neatly into a report. That’s what makes it essential.
In systems built on continuity, the most dangerous exposures are the ones no one feels responsible for. Dependency risk doesn’t wait for governance to catch up. It waits for something to stop working.
By then, you’re not managing the risk. You’re managing the surprise.
📌 Key Takeaways:
- 1️⃣ The exposure: Dependency risk is created not by what you do, but by what you assume will continue—availability, responsiveness, stability, scale.
- 2️⃣ The invisibility: It doesn’t announce itself as a risk. It presents as infrastructure—ordinary, ubiquitous, essential. That’s why institutions miss it through classification, not negligence.
- 3️⃣ The governance gap: Traditional frameworks oversee activities, controls, and owners. Dependency risk challenges all three—it’s not an activity, doesn’t map to controls, often lacks a single owner.
- 4️⃣ The reveal: Dependency becomes visible late—when escalation pathways narrow, decision rights are unclear, and options are fewer than expected. By then, you’re managing surprise, not risk.
- 5️⃣ The diagnostic: The question that surfaces dependency risk: “What are we depending on that would surprise us if it stopped working?” It doesn’t fit in reports. That’s what makes it essential.
This series began with a shift: from control to orientation, from prediction to sensemaking.
That shift changes what becomes visible.
Dependency risk is what you see when you stop organizing the world by category and start asking what you’re relying on. It’s what sensemaking reveals. It’s where the meeting after the meeting matters. It’s what translation helps you land.
It’s the practice of uncertainty in action.
Not frameworks for eliminating risk—practices for seeing it clearly, naming it honestly, and acting on it before continuity breaks and responsibility arrives too late.
Frequently Asked Questions
For readers seeking clarity on how to identify and manage dependency risk:
How is dependency risk different from third-party risk or operational risk?
Third-party risk assumes you know who the third party is and that you’re actively managing the relationship. Operational risk assumes the exposure sits within defined processes and controls. Dependency risk lives in the gap—it’s the exposure created by relying on something that isn’t clearly categorized, actively managed, or explicitly owned. A third-party vendor you monitor quarterly is third-party risk. The platform that same vendor relies on, which you’ve never inventoried because it’s “their infrastructure,” is dependency risk. The distinction isn’t academic—it’s about what gets attention and what gets assumed.
If dependency risk is so invisible, how do I start identifying it in my organization?
Start with three questions in your next strategy or governance review: (1) What must remain stable for this plan to work? (2) What are we assuming about availability, responsiveness, or continuity that we haven’t tested recently? (3) If this stopped working tomorrow, how long would it take us to notice—and how many functions would be affected? The answers reveal dependencies. Then ask: who owns the exposure? If the answer is unclear or spans multiple functions, you’ve found dependency risk. The goal isn’t to build a comprehensive inventory immediately—it’s to make the invisible discussable.
Doesn’t focusing on dependency risk just create paranoia about everything we rely on?
Only if you treat it as a reason to eliminate all dependencies, which isn’t possible or useful. The point isn’t to stop depending on systems, vendors, or processes. It’s to understand what you’re depending on clearly enough that you’re not surprised when assumptions shift. Dependency risk becomes dangerous when it’s invisible and unexamined—when continuity is assumed rather than understood. Making it visible doesn’t mean eliminating it; it means deciding consciously whether to accept it, mitigate it, or build redundancy. That’s judgment, not paranoia.
Next: Beyond the series
This concludes “The Practice of Uncertainty.”
We’ve covered the shift from control to orientation, where decisions actually happen, how to make uncomfortable truths land, and what becomes visible when you ask different questions.
The practice continues. Future posts will explore other risks that don’t fit categories, emerging patterns in AI and geopolitical exposure, and the organizational dynamics that shape how risk gets heard.
Want frameworks for identifying what you’re depending on? Subscribe to The Risk Philosopher for future insights on risk judgment and emerging threats.
Related Reading:
- Part 3: “From Truth to Traction: How to Land an Inconvenient Risk”
- Part 2: “The Meeting After the Meeting”
- Part 1: “Sensemaking Is the New Risk Leadership”
Dependency risk doesn’t wait for governance to catch up. It waits for something to stop working. By then, you’re not managing the risk—you’re managing the surprise.

